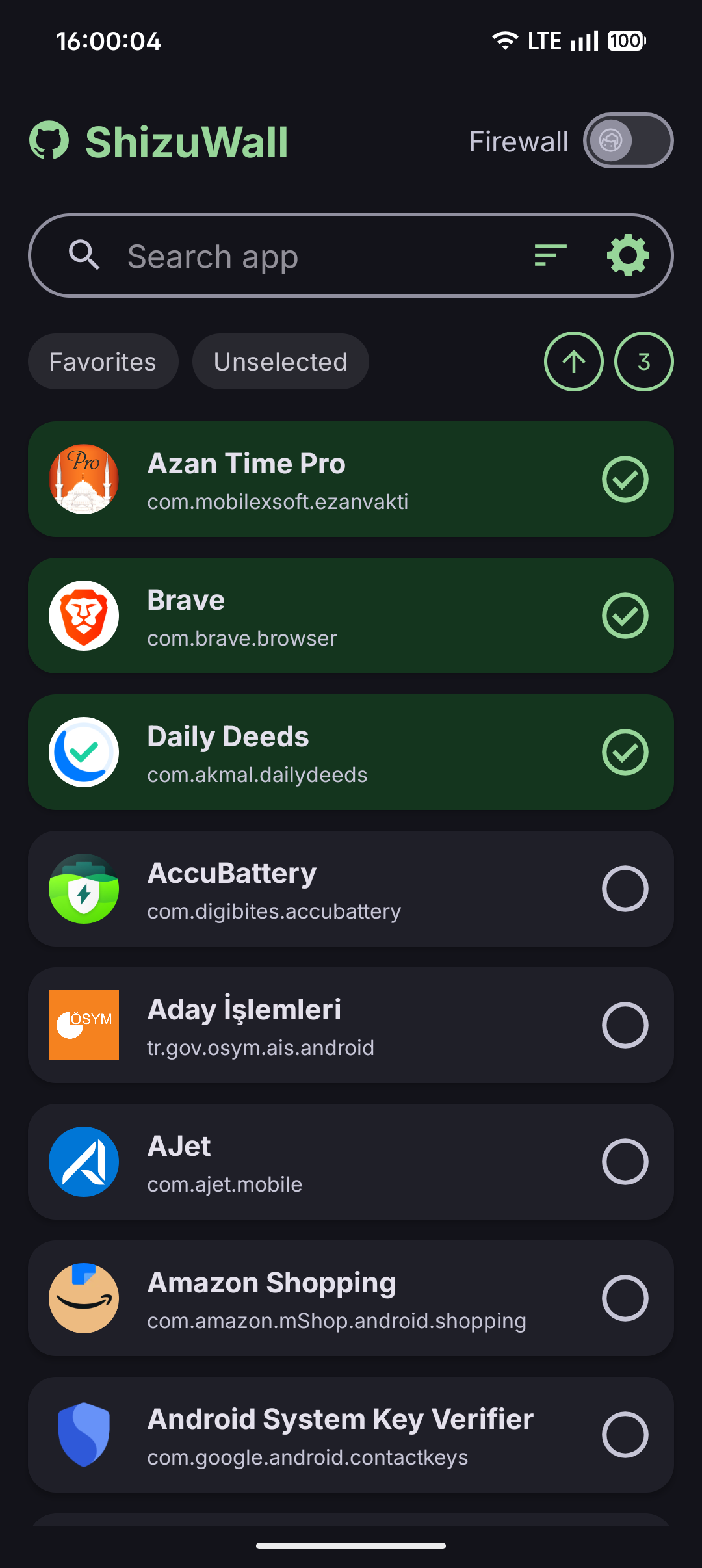
Android firewall without VPN.
Privacy-first, local-only, powered by Shizuku / local ADB daemon / Root.









- No VPN: avoids packet interception and persistent VPN tunnel side effects.
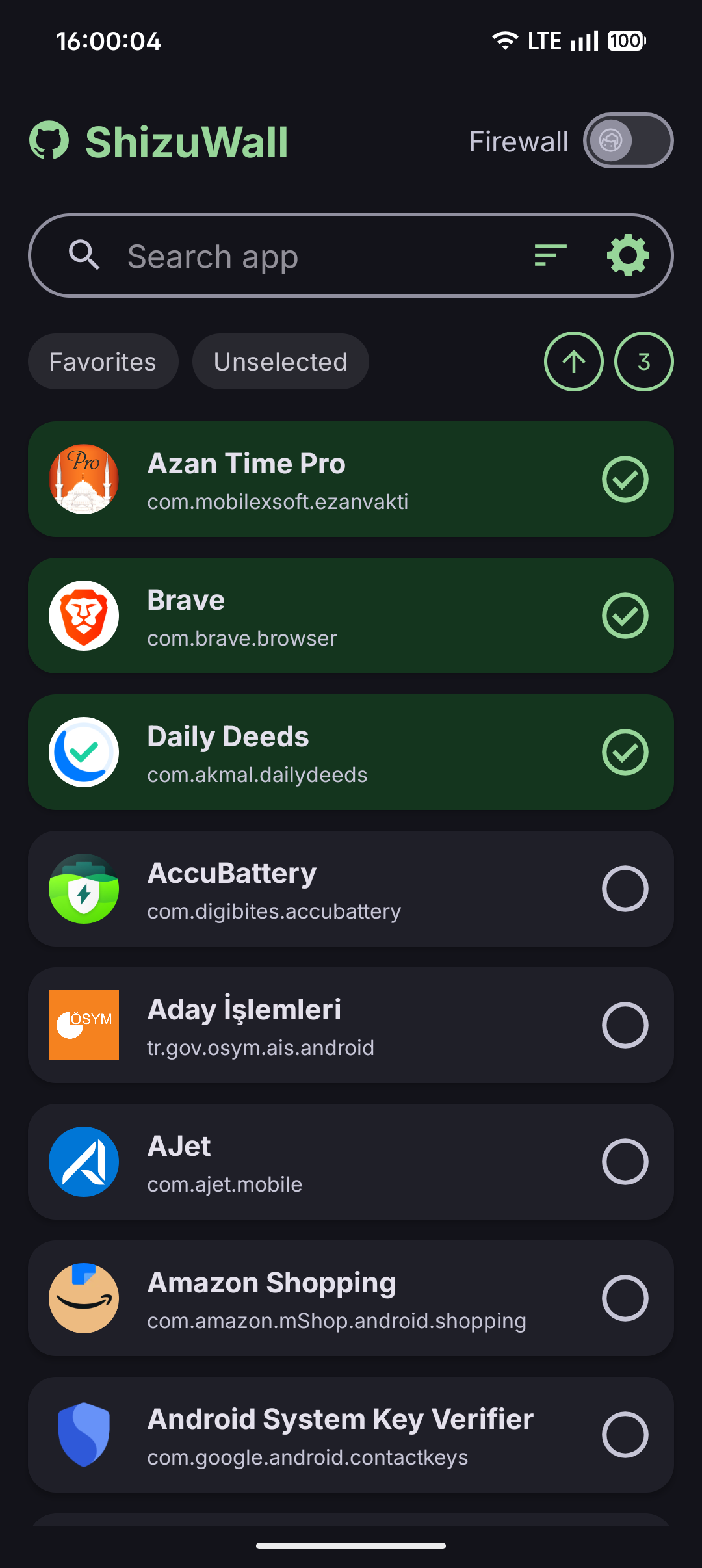
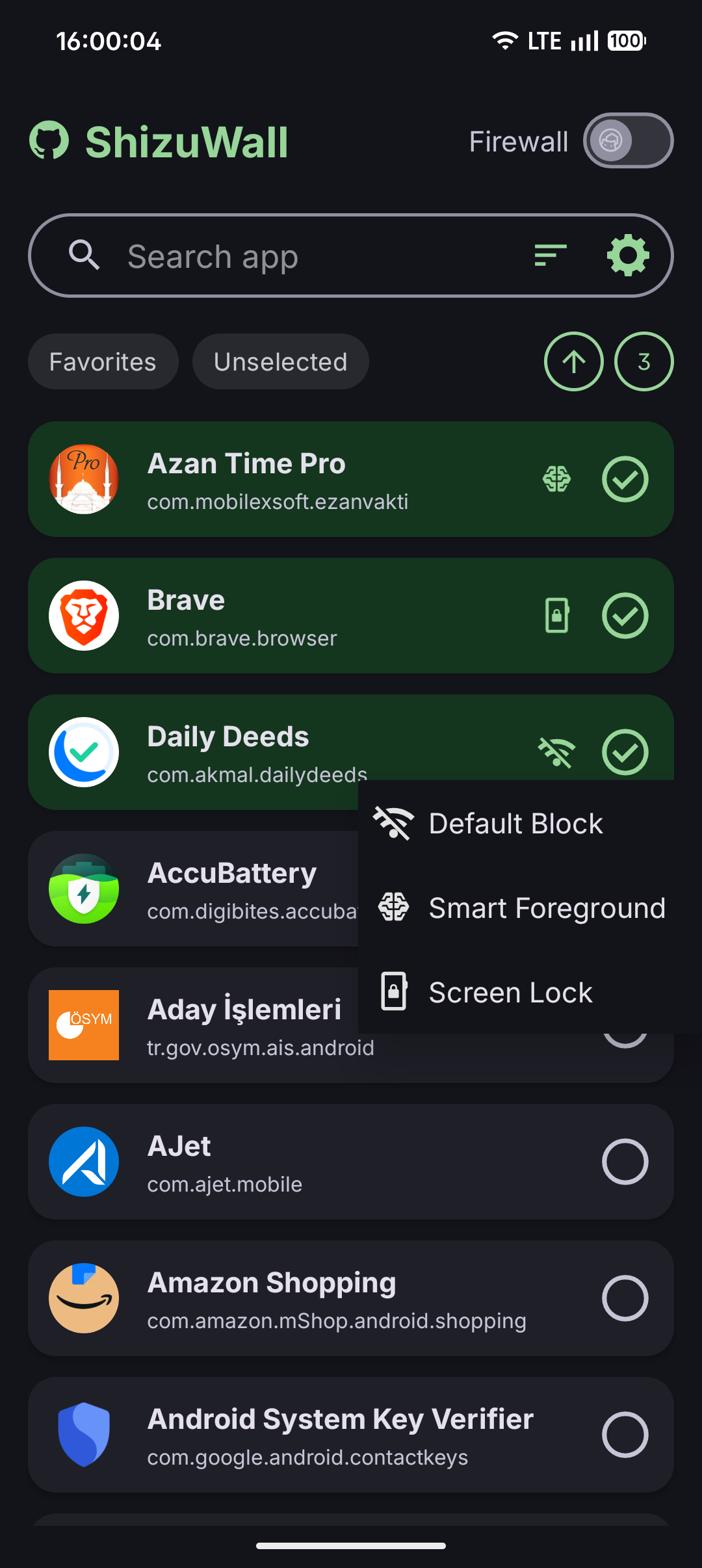
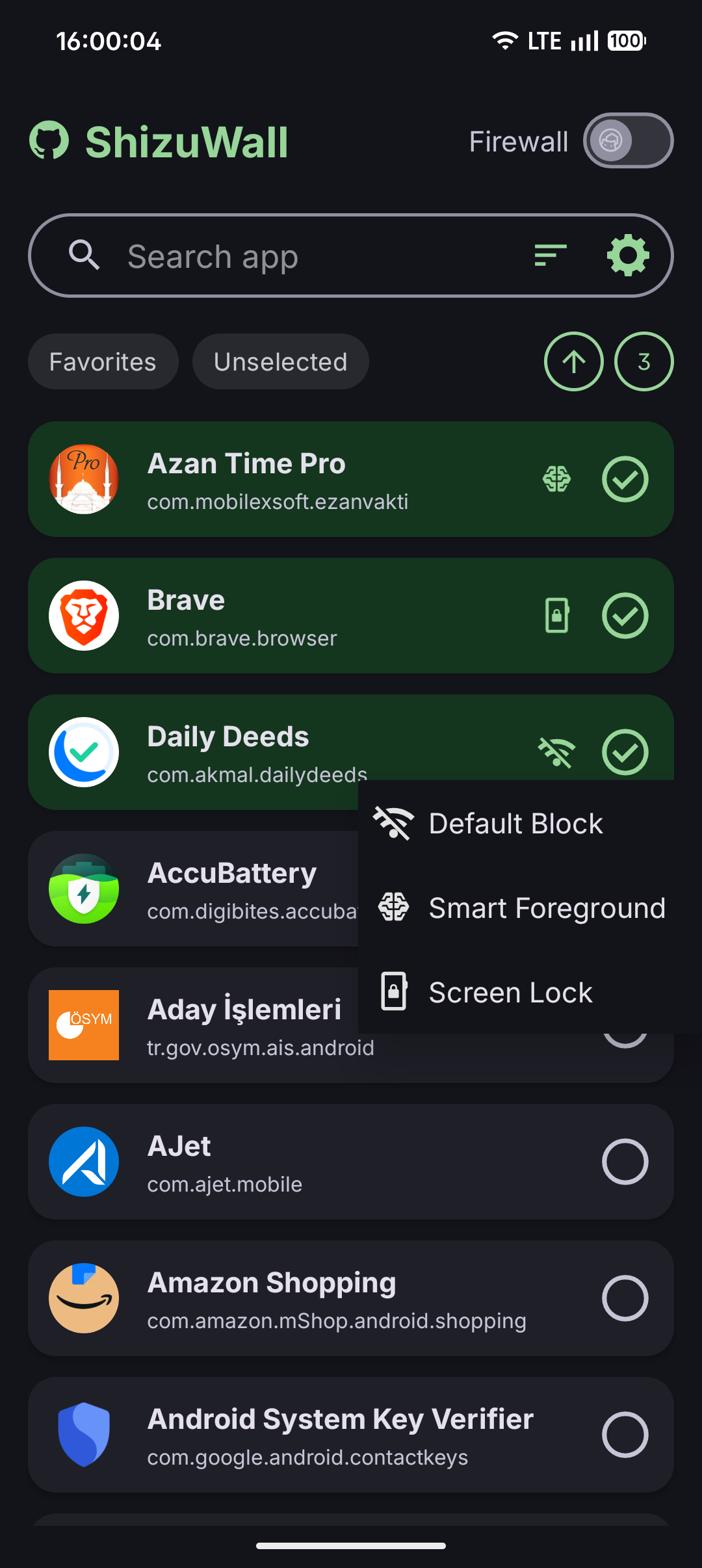
- Per-app network control: toggles app networking through Android's
connectivity chain-3 controls.
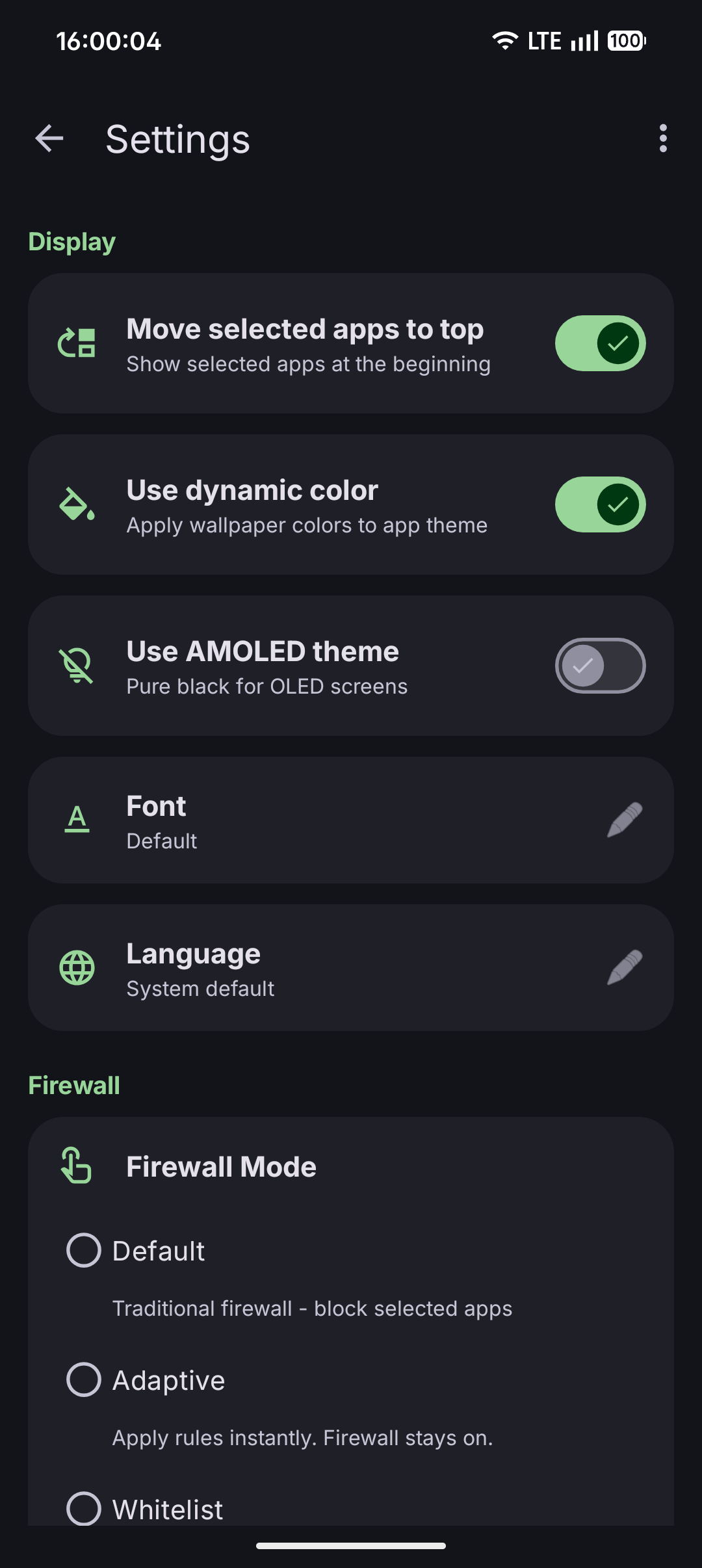
- Privacy-first by design: offline-first, no analytics, no telemetry, no tracking.
- Automation ready: supports
adb broadcast commands for scripts and task automation.
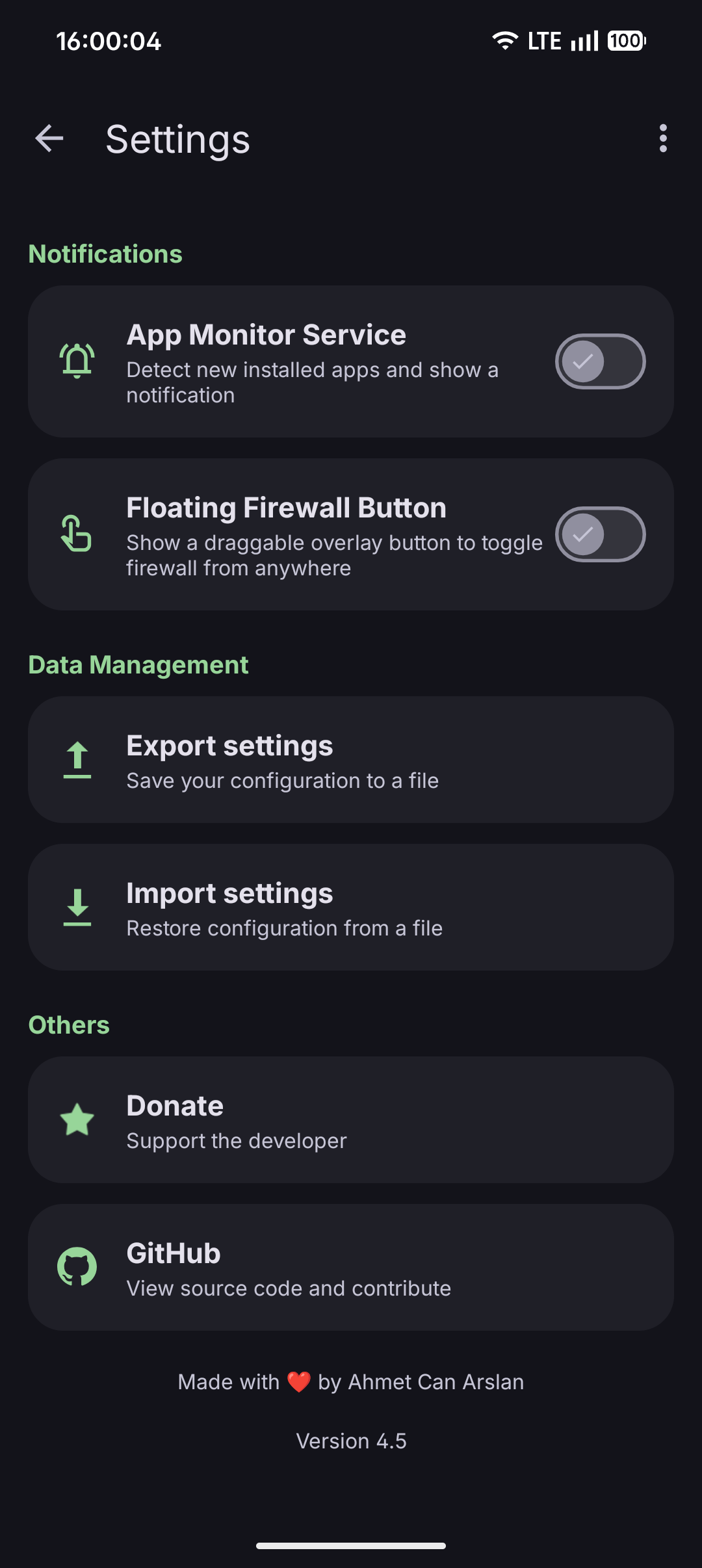
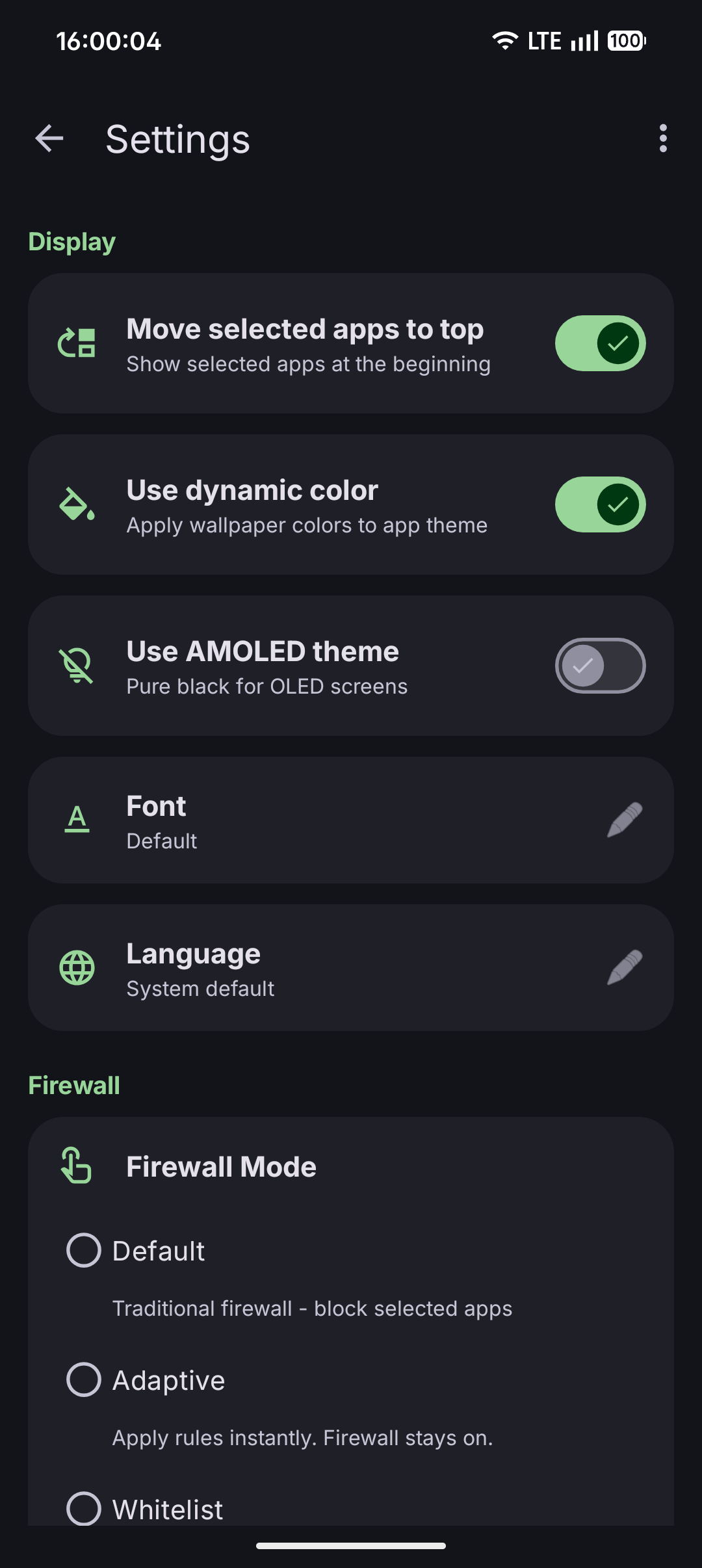
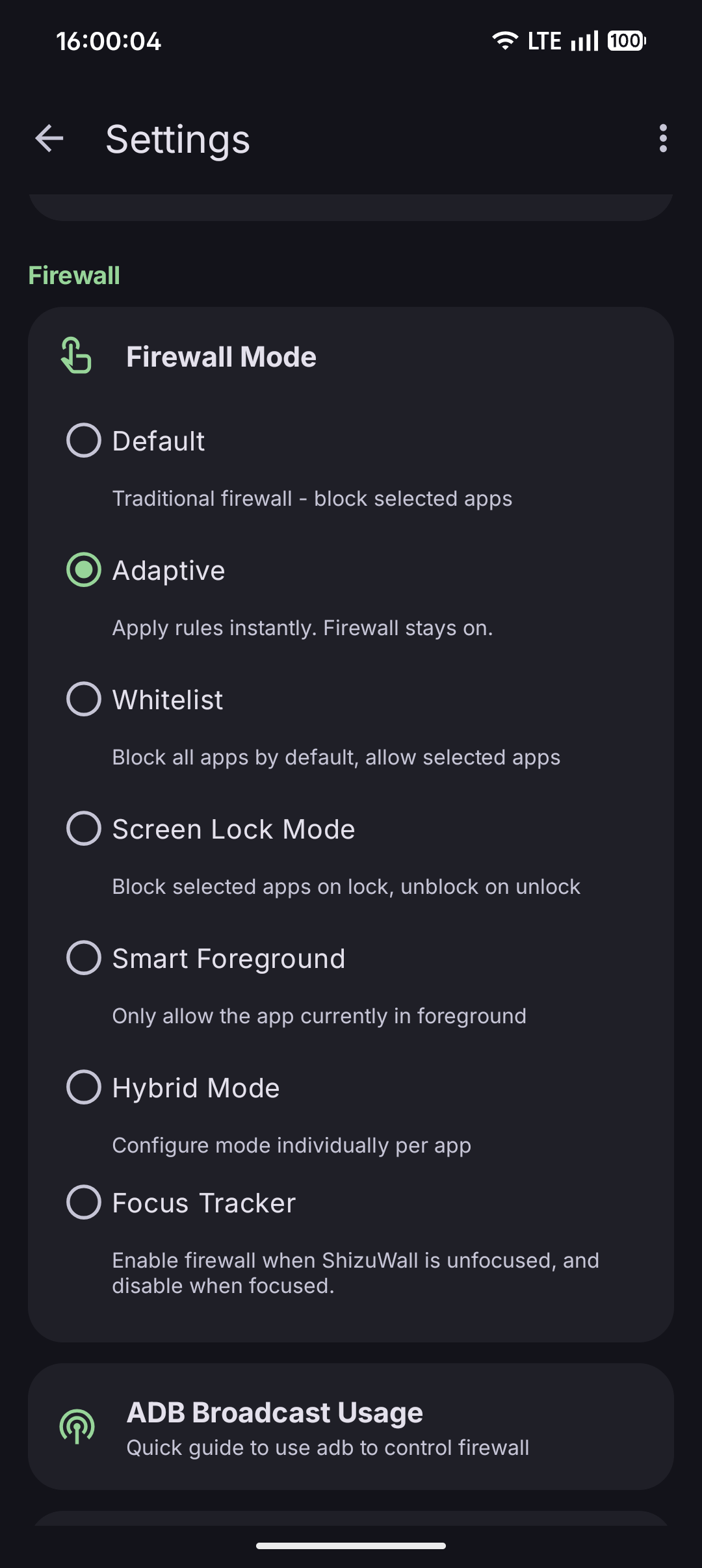
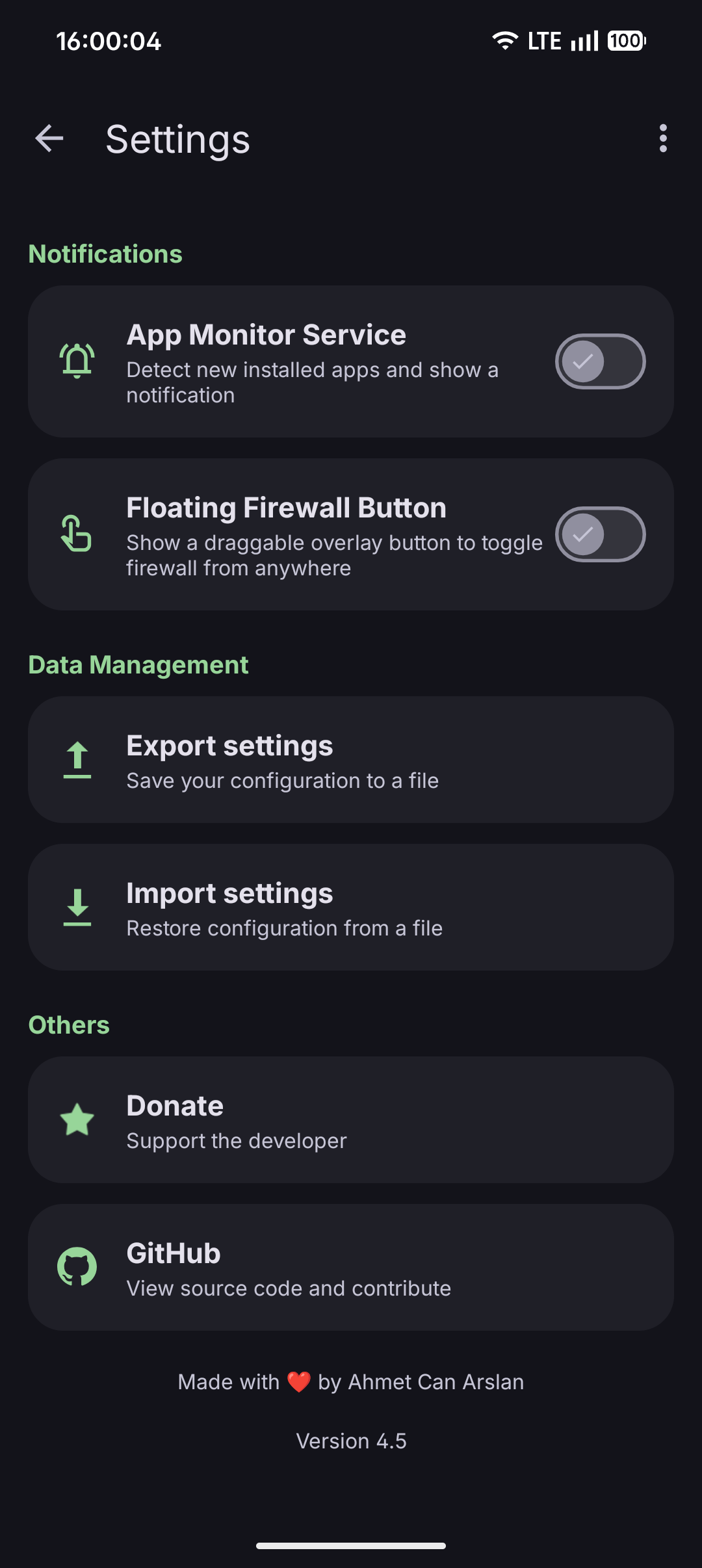
- Control Methods: ShizuWall provides three convenient ways (Quick Settings Toggle, App Widget, Floating Firewall Button) to control the firewall.
- Android 11 (API 30) or higher
- One control backend: Shizuku, local ADB daemon or root access
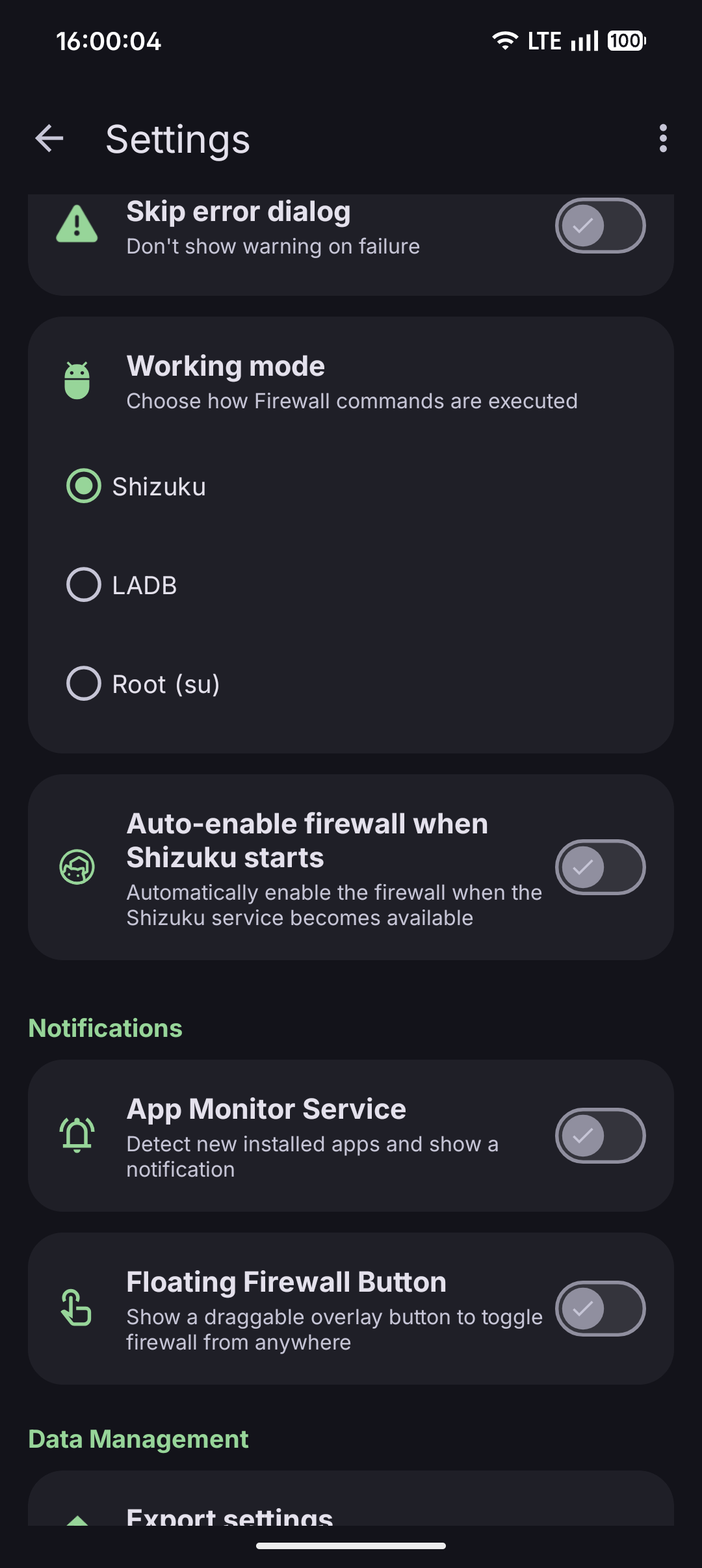
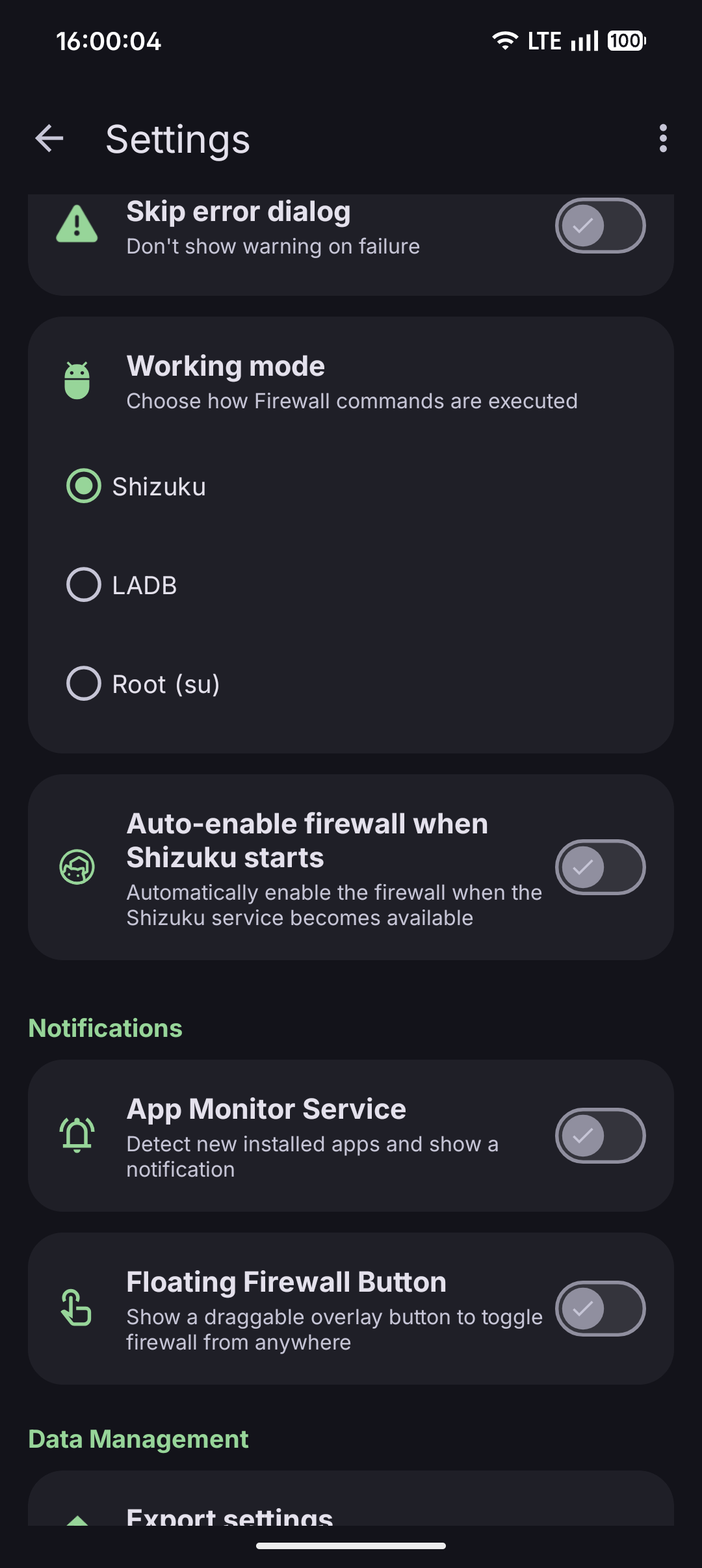
ShizuWall supports three methods to execute firewall commands:
| Method |
Description |
Setup |
| Shizuku |
Secure API that communicates with system services. Requires Shizuku app. Forks are supported. |
Install and setup Shizuku app, grant permissions |
| Root |
Direct root access. |
Root your device using standard methods |
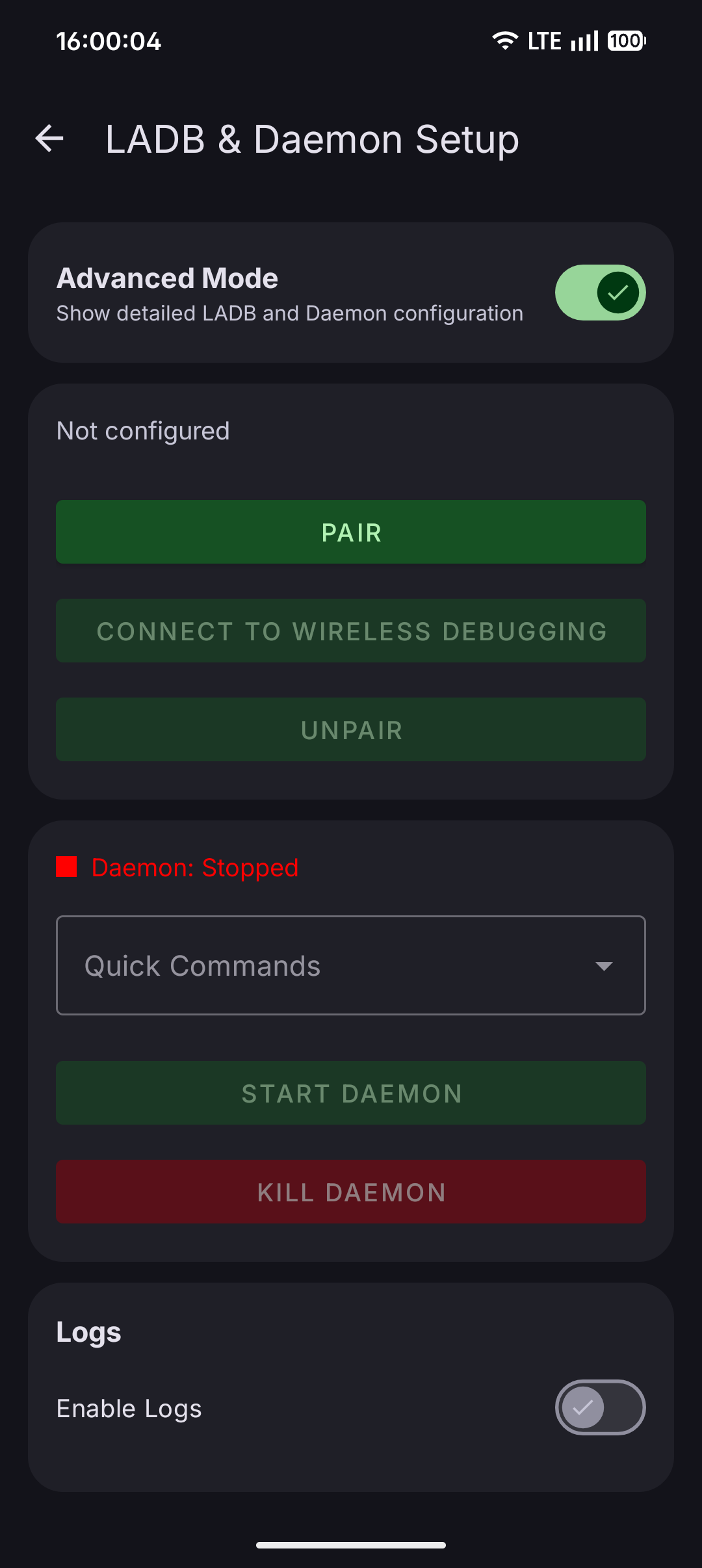
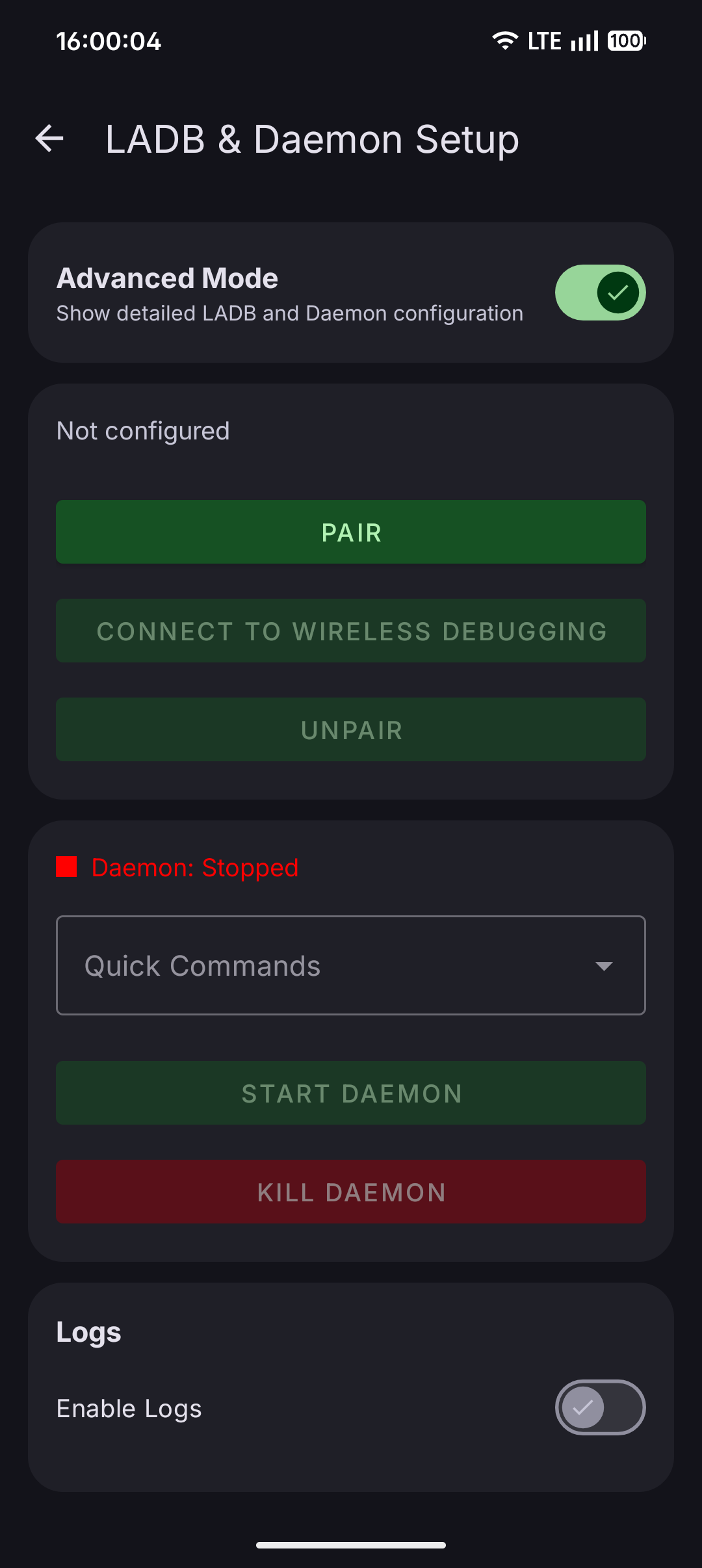
| LibADB (LADB) |
Uses the built-in "Wireless Debugging" feature of your phone to act like a computer connected via USB. This allows the app to perform advanced system changes without needing a computer, root or extra apps like Shizuku. |
Enable wireless debugging and pair in Developer Options (Guide is in app) |
ShizuWall uses Android's Chain 3 (connectivity chain) to control per-app networking. These are the platform commands executed through Shizuku or the local daemon:
<div class="highlight highlight-source-shell notranslate position-relative overflow-auto" dir="auto" data-snippet-clipboard-copy-content="# Enable firewall framework cmd connectivity set-chain3-enabled true # Block specific app cmd connectivity set-package-networking-enabled false # Unblock specific app cmd connectivity set-package-networking-enabled true # Disable firewall framework cmd connectivity set-chain3-enabled false">
# Enable firewall framework cmd connectivity set-chain3-enabled true # Block specific app cmd connectivity set-package-networking-enabled false <package.name> # Unblock specific app cmd connectivity set-package-networking-enabled true <package.name> # Disable firewall framework cmd connectivity set-chain3-enabled false
Chain 3 is an Android platform mechanism that intercepts and controls per-package network access at the system level, allowing fine-grained firewall control.
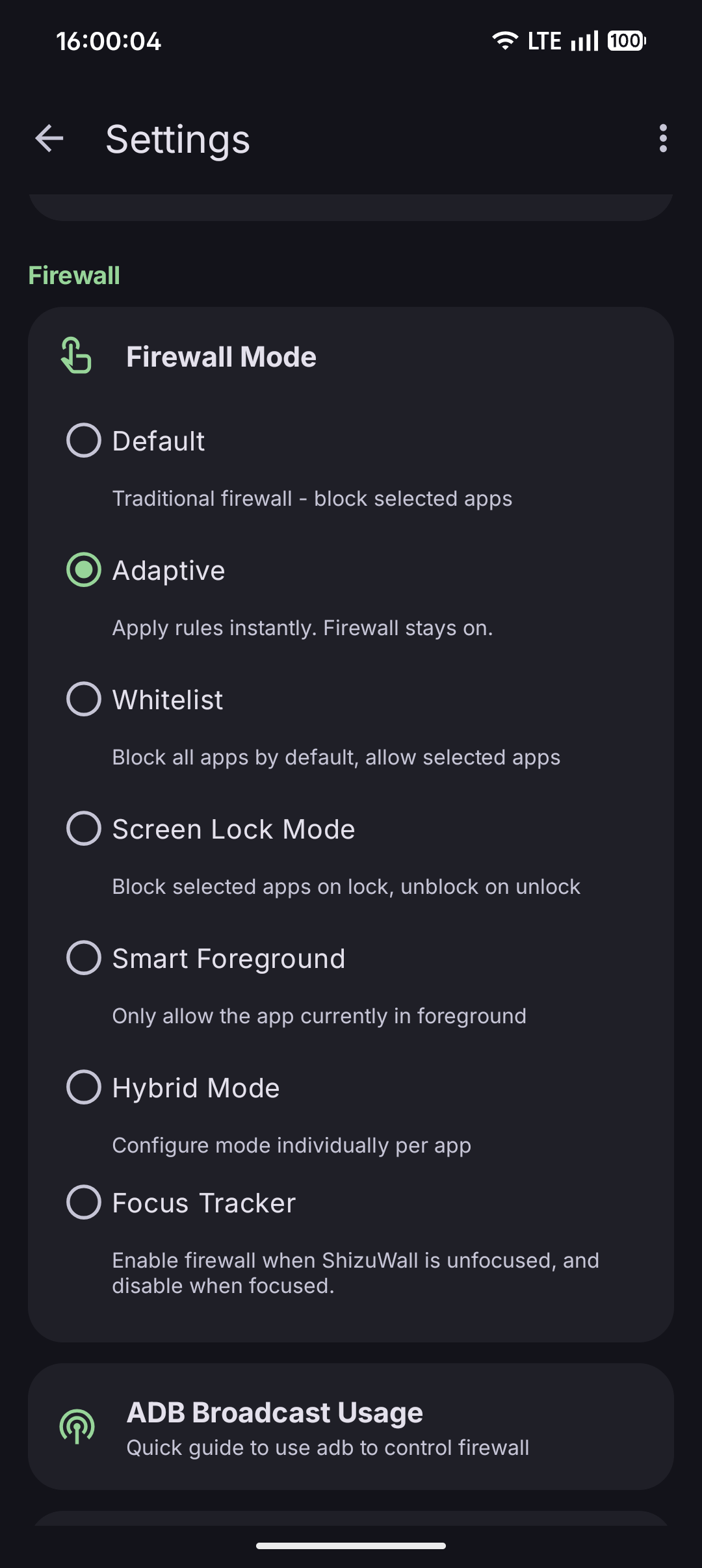
Automation (ADB Broadcast)
You can control ShizuWall from scripts and automation tools.
Action: shizuwall.CONTROL
Component: com.arslan.shizuwall/.receivers.FirewallControlReceiver
Extras
state (boolean, required): true = enable, false = disableapps (string, optional): CSV package list. If omitted, ShizuWall uses saved selected apps.
# Enable firewall for saved selected apps adb shell am broadcast -a shizuwall.CONTROL -n com.arslan.shizuwall/.receivers.FirewallControlReceiver --ez state true # Disable firewall for saved selected apps adb shell am broadcast -a shizuwall.CONTROL -n com.arslan.shizuwall/.receivers.FirewallControlReceiver --ez state false # Enable firewall for specific packages adb shell am broadcast -a shizuwall.CONTROL -n com.arslan.shizuwall/.receivers.FirewallControlReceiver --ez state true --es apps "com.example.app1,com.example.app2" # Disable firewall for specific packages adb shell am broadcast -a shizuwall.CONTROL -n com.arslan.shizuwall/.receivers.FirewallControlReceiver --ez state false --es apps "com.example.app1,com.example.app2"
One of the control backends (Shizuku, local ADB daemon or Root) must be active for broadcasts to succeed.
- Firewall rules are cleared on reboot by Android platform behavior.
- Rebooting the device resets any active ShizuWall-applied network blocks.
- The app requests
android.permission.INTERNET only for wireless debugging pairing (LibADB local daemon connection).
./gradlew assembleRelease
The on-device daemon is compiled to app/src/main/assets/daemon.bin.
Prerequisites
- Android SDK
- Java 11
d8 (Android Build Tools)
Compile
- Open scripts/compile_daemon.sh.
- Update
SDK_PATH, BUILD_TOOLS_VER, and PLATFORM_VER for your environment.
- Run:
chmod +x scripts/compile_daemon.sh ./scripts/compile_daemon.sh
ShizuWall is provided "as is" without warranty of any kind.
By using this app, you acknowledge that it relies on advanced system permissions (Shizuku/ADB/Root), and you accept all related risks. The developer is not responsible for damages such as system instability, data loss, service interruption, or side effects from blocked networking.
ShizuWall is an open-source application. The developer accepts no financial, moral, or legal responsibility for the use of this application. All responsibility belongs to the user.
Always verify which apps you block.
Licensed under GNU General Public License v3.0 (GPLv3). See LICENSE.md.
- Shizuku — API that enables privileged command execution flow.
- LibADB — Wireless debugging and daemon connection support.